Learn to Recognize and Protect Yourself from Phishing Scams
In today’s digital world, scams are becoming increasingly sophisticated. One of the most common and dangerous is the phishing scam, often delivered directly to your mobile device via text message. This guide will walk you through how to identify a phishing text, understand how these scams work, and implement crucial steps to protect your personal information.
What You’ll Learn
- How to identify the common characteristics of a phishing text message.
- The underlying tactics scammers use to trick you into revealing sensitive information.
- Practical steps to verify the legitimacy of suspicious messages.
- Essential security practices to safeguard your accounts and financial data.
Understanding Phishing Scams
Phishing, spelled with a “P-H,” is a fraudulent attempt to obtain sensitive information such as usernames, passwords, credit card details, or other personal information by disguising oneself as a trustworthy entity in an electronic communication. Text message phishing, also known as “smishing,” is particularly effective because it appears to come directly from a trusted source, like a well-known company or service, and often exploits urgency or curiosity.
How a Phishing Scam Works: A Step-by-Step Example
Let’s break down a common phishing scenario to understand the mechanics:
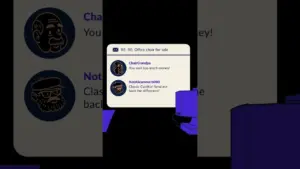
Receive a Suspicious Text Message
You receive a text message from an unknown number. The message might claim to be from a popular service, like Amazon, and reference a recent order or account activity.
For example, it could say: “Amazon order confirmed. 80-inch television on its way. To see order status, click here.”
Notice Suspicious Details
Pay close attention to the details. The message might contain typos or grammatical errors, such as “Ordror” instead of “Order.” While these errors can be a red flag, scammers sometimes intentionally include them to filter out more cautious individuals.
Click the Malicious Link (Don’t!)
The message will usually contain a link prompting you to click it to view order status, confirm details, or resolve an issue. This link is the core of the scam.
Land on a Fake Login Page
Clicking the link will direct you to a website that looks almost identical to the legitimate login page of the company it’s impersonating (e.g., Amazon). It will ask you to log in with your email and password.
Enter Your Credentials
If you enter your login information, the scammer immediately captures your username and password. This information is then used to access your account.
Information Compromised
Once the scammer has your login details, they can access your account. This often includes associated payment information, allowing them to make unauthorized purchases or steal financial data. In the example above, there was no 80-inch TV; the goal was simply to steal your login and payment information.
Why Do People Fall for Phishing Scams?
Phishing scams are effective because they often leverage trust and urgency. They exploit our reliance on well-known institutions and aim to elicit a quick response before we have time to think critically. Scammers strike while the iron is hot, preying on the assumption that a message from a familiar source is legitimate.
How to Protect Yourself from Phishing Texts
Protecting yourself from these scams requires vigilance and a few key security practices:
Be Skeptical of Unsolicited Messages
Always approach unexpected text messages, especially those asking for personal information or urging immediate action, with caution. If a message seems too good to be true or creates a sense of panic, it likely is.
Look for Typos and Grammatical Errors
While not always present, misspellings, odd phrasing, or unusual formatting can be strong indicators of a scam. Legitimate companies usually have their communications professionally reviewed.
Never Click Suspicious Links
Avoid clicking on links in text messages from unknown or suspicious sources. Even if the sender appears familiar, if the message is unexpected or seems off, do not click the link.
Verify Independently
The most crucial step is to verify the message’s authenticity through a separate, trusted channel. If you receive a suspicious text about an account or order, do not use the contact information or links provided in the text. Instead, go directly to the company’s official website by typing the address into your browser, or call their official customer service number (found on their website or your account statements) to inquire about the message.
Expert Tip: The principle here is “Trust, but verify.” Always confirm the legitimacy of a message by contacting the purported sender through a known, official channel.
Do Not Share Personal Information
Never provide your login credentials, passwords, credit card numbers, social security number, or other sensitive personal information in response to a text message or email. Legitimate companies will rarely ask for this information via text or unsolicited email.
Keep Software Updated
Ensure your phone’s operating system and security software are always up-to-date. Updates often include patches for security vulnerabilities that scammers might try to exploit.
Change Your Passwords Regularly
If you suspect you may have fallen victim to a phishing scam or shared your credentials, change your passwords immediately for the affected account and any other accounts that use the same password. Use strong, unique passwords for each online service.
Conclusion
Phishing scams are a persistent threat, but by understanding how they work and employing simple verification techniques, you can significantly reduce your risk. Stay alert, trust your instincts, and always verify suspicious communications through official channels to keep your personal and financial information secure.
Source: Scams and Fraud v2 mobile version pt 4 2 (YouTube)