Understanding Authentication and Authorization
In the world of web development and security, the terms ‘authentication’ and ‘authorization’ are often used interchangeably. However, they represent two distinct and crucial steps in securing user access to your applications. This guide will break down the differences between authentication and authorization, explaining what each process entails and how to implement them correctly using appropriate HTTP status codes.
What You Will Learn
- The fundamental difference between authentication and authorization.
- How to identify examples of authentication in practice.
- When and why to use the 401 HTTP status code.
- The role of authorization in defining user capabilities.
- How to recognize different authorization models.
- When and why to use the 403 HTTP status code.
- The importance of this two-step process for clear communication and security.
Prerequisites
- Basic understanding of web development concepts.
- Familiarity with HTTP requests and responses.
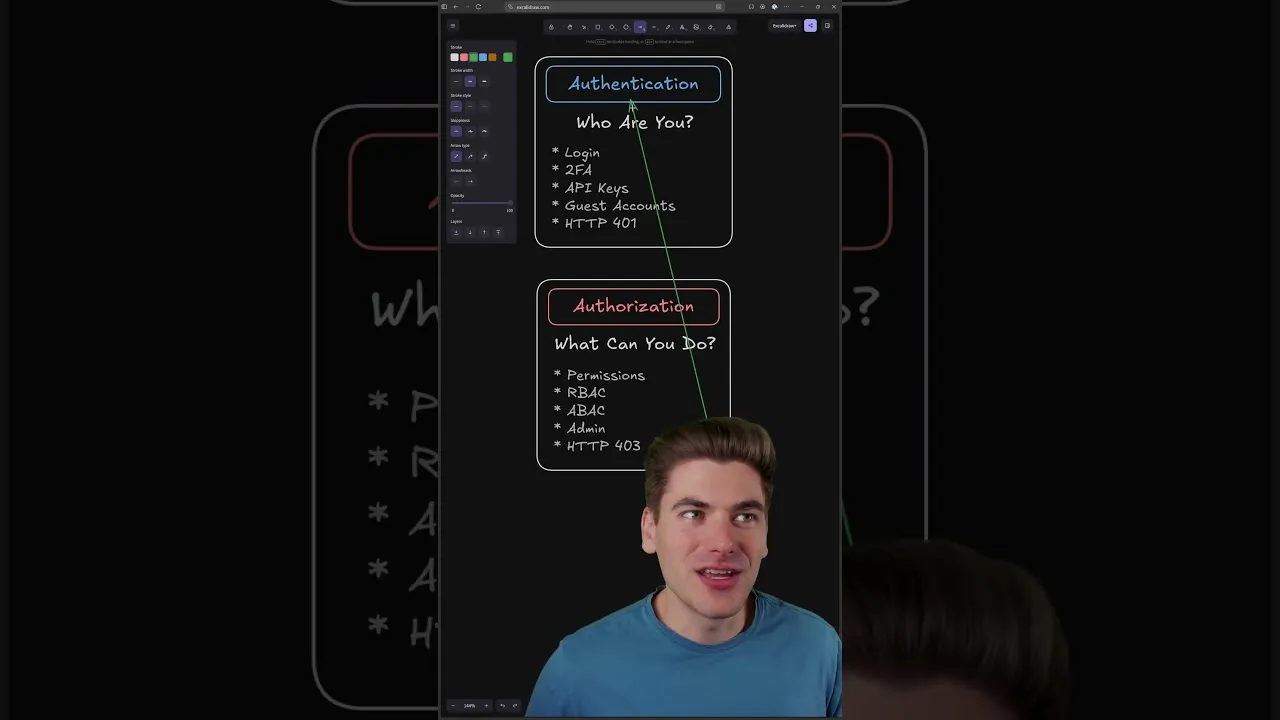
Step 1: Understanding Authentication
Authentication is the very first step in the security process. Its primary goal is to verify the identity of a user or system. In simpler terms, it answers the question: ‘Who are you?’
Examples of Authentication:
- Login Credentials: When a user enters a username and password, they are attempting to authenticate themselves.
- Two-Factor Authentication (2FA): This adds an extra layer by requiring a second form of verification, like a code from a mobile app or an SMS message, further confirming identity.
- API Keys: When a service or application uses an API key, it’s a form of authentication to verify that the requesting entity is legitimate and has permission to access the API.
- Guest Accounts: Even a ‘guest’ account is a form of authentication. While it signifies limited access, the system is still verifying that the user is allowed to be present in a guest capacity.
Handling Authentication Failures
If a user or system fails the authentication process, meaning their identity cannot be verified, it is critical to respond with the correct HTTP status code. The standard for this is the 401 Unauthorized status code. This code signals to the client that the request lacks valid authentication credentials, and therefore, the server cannot fulfill it because it doesn’t know who is making the request.
Step 2: Understanding Authorization
Once authentication is successfully completed, the next logical step is authorization. This process determines what actions an authenticated user is allowed to perform within the system. It answers the question: ‘What can you do?’
Authorization Mechanisms:
- Permission Systems: This is the broad concept of defining what actions are permitted.
- Role-Based Access Control (RBAC): Users are assigned roles (e.g., ‘admin’, ‘editor’, ‘viewer’), and each role has specific permissions associated with it.
- Attribute-Based Access Control (ABAC): Access is granted or denied based on a combination of attributes related to the user, the resource, and the environment.
- Admin Accounts: An administrator account is a specific example of a role with extensive permissions.
Handling Authorization Failures
When an authenticated user attempts to perform an action for which they do not have the necessary permissions, you should respond with the 403 Forbidden HTTP status code. This code indicates that the server understands the request but refuses to authorize it because the authenticated user lacks the required permissions. It’s crucial to distinguish this from a 401; a 401 means ‘I don’t know who you are,’ while a 403 means ‘I know who you are, but you’re not allowed to do that.’
The Two-Step Process: Authentication Then Authorization
It’s essential to recognize that authentication and authorization are sequential. You cannot effectively authorize someone if you don’t first know who they are. The process flows like this:
- Authentication: Verify the identity of the user. This applies universally, even for guest access.
- Authorization: Based on the verified identity, determine the user’s permissions and what actions they can perform.
Why This Distinction Matters
Clearly understanding and implementing the difference between authentication and authorization leads to several benefits:
- Clearer Communication: When discussing security protocols and issues, using the correct terminology prevents confusion among developers, stakeholders, and even in documentation.
- Robust Security: A well-defined separation of concerns makes it easier to build secure systems. You can focus on robust identity verification (authentication) and then implement granular control over actions (authorization).
- Easier Debugging: When a user encounters an access issue, knowing whether it’s an authentication problem (login failed, invalid credentials) or an authorization problem (logged in but can’t access a feature) significantly speeds up troubleshooting.
Expert Tip
Always strive to provide the most specific error message possible without revealing sensitive information. For example, instead of just saying ‘Access Denied,’ consider if it’s a 401 (invalid credentials) or a 403 (insufficient permissions) and communicate that to the client appropriately.
Further Learning
To delve deeper into the implementation details of authorization, including setting up role-based access control (RBAC) and attribute-based access control (ABAC) from scratch, please refer to the linked video that provides a comprehensive guide on these advanced topics.
Source: The 2 Parts of Auth You Need To Know (YouTube)