Understanding Denial of Service Attacks: A Practical Demonstration
In the realm of cybersecurity, understanding attack vectors is crucial for effective defense. A recent demonstration, though cautioned against for ethical and legal reasons, offered a clear, hands-on look at how Denial of Service (DoS) and Distributed Denial of Service (DDoS) attacks work. The experiment involved a user intentionally overwhelming their own web server to illustrate the principles behind these common cyber threats.
The Basics of Denial of Service (DoS)
A DoS attack aims to make a machine or network resource unavailable to its intended users. This is typically achieved by flooding the target with excessive traffic or sending it malformed requests, causing it to crash or become unresponsive. The initial demonstration focused on a simple ping flood, a basic form of DoS.
The user set up a web server and monitored its performance by pinging it from another server. Pinging, or sending Internet Control Message Protocol (ICMP) echo requests, is a standard diagnostic tool used by IT professionals to check network connectivity and server health. When a server responds quickly to these pings, it indicates it is healthy and accessible. The latency, or the time it takes for a ping request to receive a response, serves as a key performance indicator.
Attempting a Single-Source DoS Attack
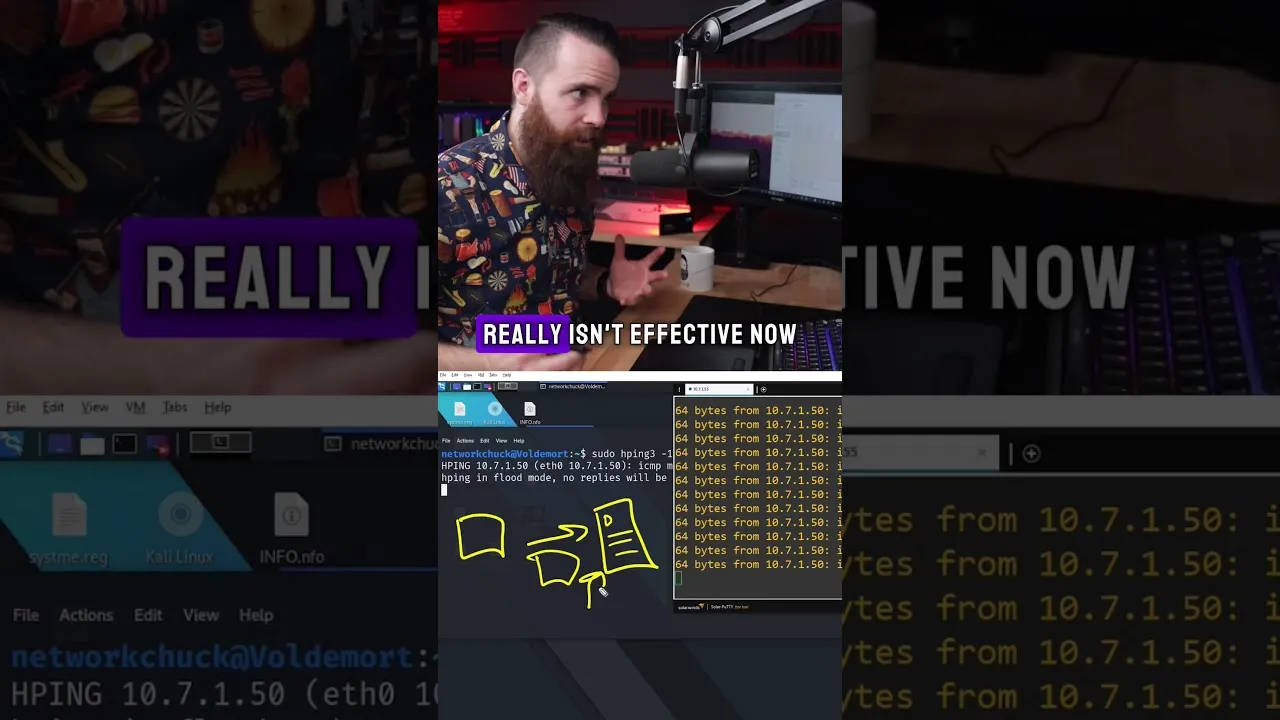
The first attempt involved overwhelming the server with a high volume of pings from a single source. Using a popular hacking tool called hping3 with the -1 (ICMP flood) switch, the user directed a flood of requests to their server’s IP address. The goal was to saturate the server’s bandwidth or processing capacity.
However, the results were underwhelming. Monitoring the ping latency to the server showed little to no significant change. The server, equipped with ample bandwidth, was easily able to handle the volume of requests from one machine. This highlights a key limitation of simple, single-source DoS attacks: they are often easily mitigated by modern server infrastructure with sufficient resources.
Introducing Distributed Denial of Service (DDoS)
The demonstration then shifted to a more sophisticated and effective threat: the Distributed Denial of Service (DDoS) attack. Unlike a DoS attack that originates from a single point, a DDoS attack utilizes multiple compromised computer systems—often referred to as a botnet—to flood the target with traffic simultaneously.
By initiating ping floods from multiple sources concurrently, the user observed a dramatic increase in latency. The time taken for ping requests to be processed jumped from sub-millisecond levels to as high as 19 milliseconds on the local network. While this might seem small in absolute terms, such an increase is considered significant, especially within a controlled local area network (LAN). This multiplication of attack vectors is what makes DDoS attacks so potent.
How DDoS Attacks Work
DDoS attacks exploit the collective power of numerous compromised devices. These devices, controlled remotely by an attacker, are instructed to send a massive amount of traffic or requests to a specific target. The sheer volume of data overwhelms the target’s resources, such as its network bandwidth, processing power, or even application-level services, rendering it inaccessible to legitimate users.
The Ping Flood (ICMP Flood) Vulnerability
The specific attack demonstrated was a ping flood, which leverages the ICMP protocol. Attackers exploit the fact that servers are designed to respond to ping requests to ensure they are online. By overwhelming the server with these requests, the attacker aims to consume the server’s resources needed to handle legitimate traffic.
Defeating the Ping Flood
The demonstration also touched upon the relative ease with which this particular type of attack can be countered. The presenter noted that a simple ping flood, like the one shown, can be defeated by disabling ICMP (ping) responses on the target server. If the server is configured not to respond to ping requests, the attack becomes ineffective.
Why This Matters
While the demonstration was a controlled experiment on a personal server, the principles illustrated are directly applicable to real-world cyber threats. DDoS attacks remain a significant concern for businesses, governments, and online services worldwide. They can disrupt critical infrastructure, cause substantial financial losses due to downtime, and damage brand reputation.
Understanding how these attacks are executed, from basic ping floods to more complex botnet-driven assaults, is the first step in developing robust defense strategies. These strategies often involve:
- Traffic Scrubbing Services: Specialized services that filter malicious traffic before it reaches the target network.
- Firewall Configuration: Implementing and configuring firewalls to block suspicious traffic patterns and protocols.
- Rate Limiting: Limiting the number of requests a server will accept from a single IP address within a given time frame.
- Network Infrastructure: Ensuring sufficient bandwidth and processing capacity to withstand moderate traffic spikes.
- Intrusion Detection and Prevention Systems (IDPS): Tools that monitor network traffic for malicious activity and can automatically block threats.
The demonstration served as a stark reminder that while the tools and techniques of cyber attackers evolve, the fundamental goal remains the same: to disrupt availability. For defenders, continuous vigilance, understanding of attack methodologies, and implementation of layered security measures are paramount.
Disclaimer
It is crucial to reiterate that performing DoS or DDoS attacks on any system without explicit, written permission from the owner is illegal and can result in severe legal penalties, including jail time. This demonstration was for educational purposes only and should not be replicated without proper authorization and ethical considerations.
Source: I DDoS'd myself (don't do this) (YouTube)