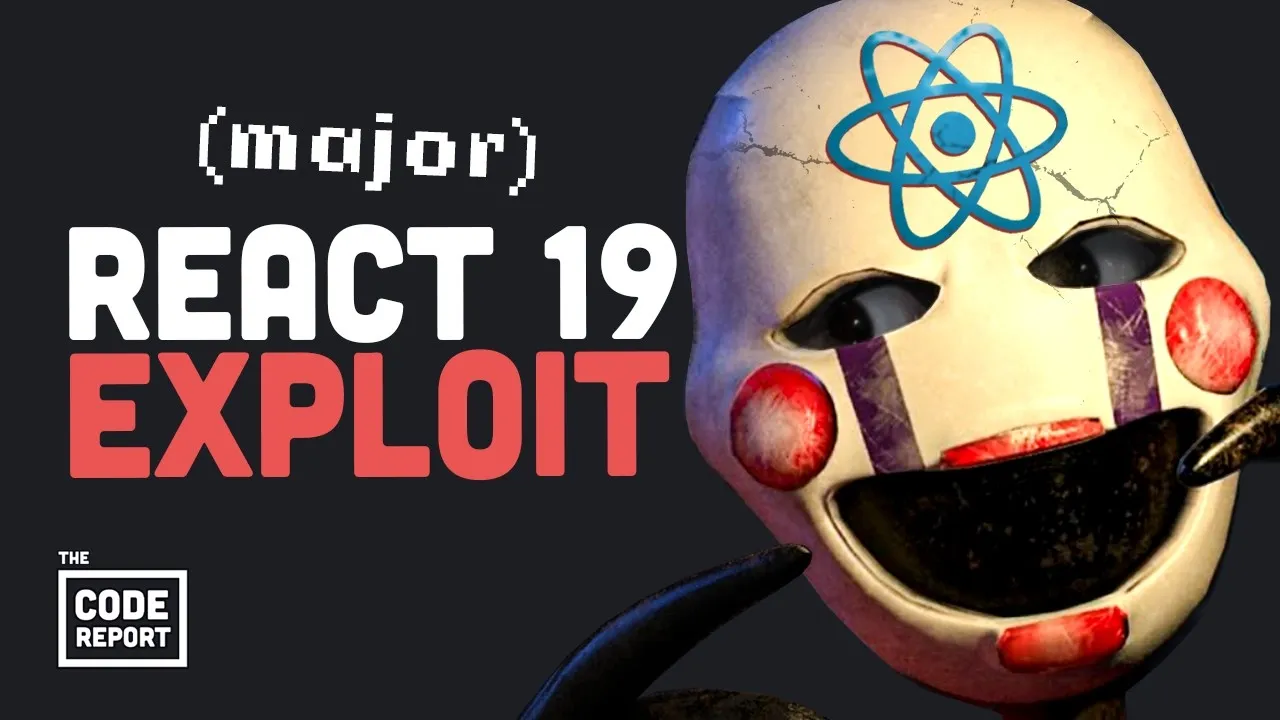
React’s Server Components Vulnerable to ‘React2Shell’ Exploit
The JavaScript ecosystem is reeling from the discovery of a critical vulnerability, dubbed ‘React2Shell,’ affecting the widely-used React.js framework. This exploit, carrying a maximum severity rating of 10.0, targets the framework’s Server Components and their underlying ‘Flight Protocol,’ posing a significant risk to millions of modern web applications.
Understanding the ‘React2Shell’ Vulnerability
The vulnerability, officially designated CVE-2025-55182, allows attackers to gain shell access to a server through a single HTTP request, bypassing authentication and normal security protocols. This is comparable in potential impact to the infamous ‘Log4Shell’ vulnerability that plagued the Java ecosystem in 2021, which led to widespread attacks and significant global disruption.
At its core, the exploit leverages a flaw in how React handles the deserialization of untrusted input within its Server Components. Server Components are designed to render parts of an application on the server before sending them to the client, a process analogous to pre-fabricating shed components in a factory before assembly on-site.
The React Flight Protocol is the mechanism by which this server-rendered data is serialized and transmitted to the browser. The vulnerability arises when the server deserializes malicious ‘flight payloads.’ These payloads can construct object graphs that should not exist in legitimate code paths, enabling attackers to manipulate the server’s runtime environment. This can lead to indirect calls to dangerous APIs or direct execution of arbitrary code on the server.
“The classic deserialize untrusted input, then treat it like it came from your best friend, then get devastating remote code execution as the result,” explains one analysis of the exploit. Attackers can exploit this to turn a compromised server into a cryptominer or worse, all without needing any prior authentication or session credentials.
Widespread Impact and Immediate Threats
The concern is amplified by the widespread adoption of React Server Components, particularly within popular frameworks like Next.js. Many developers, especially those building modern web applications, default to these tools, making a large portion of the web infrastructure potentially vulnerable.
Security firms reported observing real-world attack traffic targeting this vulnerability within hours of its public disclosure. Amazon, for instance, noted attack attempts linked to Chinese hacking groups almost immediately after the exploit became known. Estimates suggest over 2 million servers could be vulnerable, with active scanning and exploitation attempts underway.
Identifying and Mitigating the Risk
Developers can check if their applications are affected by running a specific command to identify vulnerable versions of React Server Components packages. The advice for affected developers is urgent: update vulnerable code as quickly as possible.
The exact packages and versions affected include [Specific package names and versions would be listed here if available in the transcript]. Ignoring this vulnerability is akin to performing an ‘npm install malware,’ as the transcript starkly puts it, with potential consequences ranging from data breaches to complete server compromise and costly recovery efforts.
Introducing GenSpark: An AI-Powered Solution for Developers
Amidst the scramble to address this critical vulnerability, tools like GenSpark are being highlighted as potential aids for developers. GenSpark is an AI workspace designed to orchestrate multiple AI models to accelerate development tasks.
Instead of manually interacting with various AI models, users can instruct GenSpark to achieve a desired outcome. The platform then uses a combination of AI agents to produce a polished result. For developers, GenSpark offers a browser-based environment for building applications, from simple landing pages to full-stack web apps, with easy deployment options on platforms like Cloudflare.
The service also allows integration with external tools such as Slack and Google Drive, enabling GenSpark to perform actions on behalf of the user and act as a central hub for work. A free trial of GenSpark is available via a provided link.
Why This Matters
The ‘React2Shell’ vulnerability underscores a persistent challenge in software development: the secure handling of data and the potential for critical flaws to emerge in widely adopted technologies. The exploit’s ability to grant unauthenticated remote code execution is a worst-case scenario for any web application, potentially leading to data theft, service disruption, and reputational damage.
The incident serves as a stark reminder for developers and organizations to stay vigilant about security, promptly apply patches, and continuously assess the security posture of their technology stacks. The rapid exploitation following public disclosure highlights the speed at which threats can materialize in the current cybersecurity landscape.
Source: React.js shell shocked by 10.0 critical vulnerability… (YouTube)